|
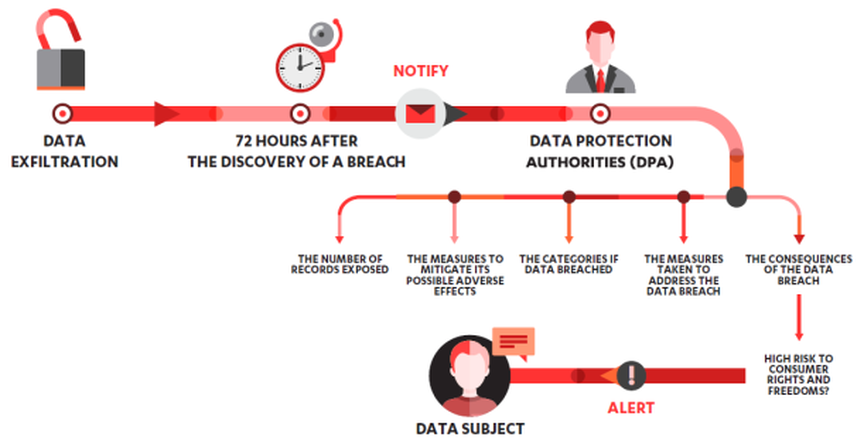
The European Union EU) adopted a new law in 2016. It affects every company with customers residing in the EU. It comes into force on 25th May 2018, which is just over a week away. It is called the General Data Protection Regulation, or GDPR for short. But what does it mean, and should companies be worried? Firstly it address a number of key areas around the privacy of data to EU citizens, in relation to the storage, processing and handling of personal data. Personal data includes data that can identify the individual directly. This can include the following:
I've simplified and summarised the key points of the GDPR legislation below:
The overall effect is to provide improved protection for EU citizens and to unify the laws across the EU. This puts onus on those businesses, including the cloud providers to ensure that data is processed fairly and in accordance with the law. There are a number of sanctions that can be enforced, depending on the nature of the breach:
So what should companies do? Firstly they need to seek legal advice from an expert in European Union law to understand the potential impacts and next steps. Next steps are to perform an audit of their business processes and how they store data to understand their current state. Then they need to perform some analysis on the law, with their legal expert to interpret the law and create a series of overarching requirements. These requirements then need to be solidified into a series of solutions. Here is a great example of how market-leading SaaS cloud provider Xero, are approacing their GDPR obligations in relation to their financial accounting package: It's so important in all this work to ensure that the IT, security, legal and business departments are all working together closely to work through the issues and implement the solutions.
Want to know more about how you can secure your data and ensure you are following the latest best practices? Consider taking a Certified Cloud Security Professional certification, leading to an ISC2 examination. I'd be glad to coach you through your questions and help expand your knowledge of all things security: www.alctraining.com.au/course/ccsp-certified-cloud-security-professional/
0 Comments
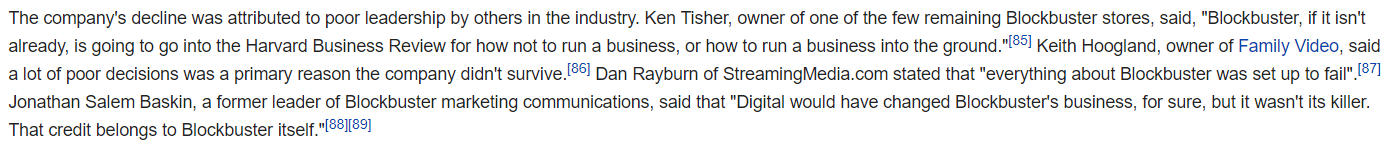
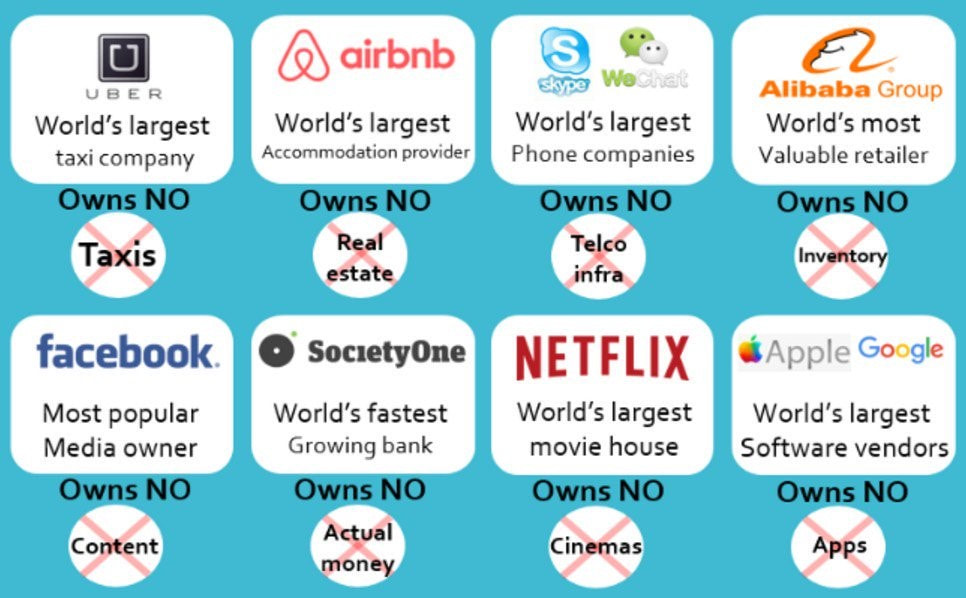
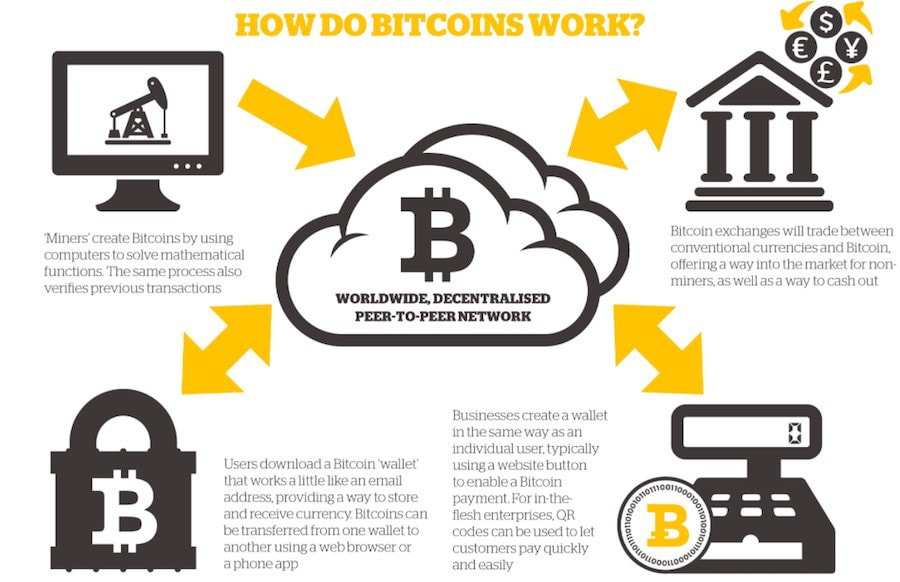
8/3/2018 0 Comments Do BitCoin and BlockChain Cryptocurrencies require Legal regulation and Consumer Protection?I’m a huge fan of utilising the latest and greatest disruptive technologies. Not just because they improve competition between businesses, but usually because they offer a lower price point and some form of additional value. Let’s take Netflix - ~$12AUD per month and I tend to watch 6-8 films per month, mainly with my kiddies. Compare that to a cinema where a film costs ~$20AUD, however it is on a big screen with surround sound, but it’s expensive to take the kiddies. Or compare with a video rental of around ~$5AUD per film when you could actually rent DVD videos from Blockbuster Video….that’s another story in itself on Wikipedia: Another example is Uber - $22AUD per trip into the Brisbane CBD, compared to $35AUD for a taxi ride. Uber’s are cheaper, cleaner, don’t smell and the drivers are friendlier. Here is a quick glance of a range of new disruptive companies that have emerged over the past few years. Important to note that they don’t actually own the product that is consumed by the customer, they utilise 3rd parties to provide the products as part of their value stream. So…. does this pattern hold true for all disruptive technologies? Let’s look at Blockchain technologies, specifically the purchasing of Bitcoin. This one is a little different, because it’s yet to fully disrupt, displace or compete with the Australian Dollar (AUD) or the ASX share market. Is it cheaper…difficult to compare as price is not relevant here…. does it provide more value…?....not really, if you consider that I can’t spend Bitcoin in many places, unlike my credit card or cash which is accepted everywhere. Both in Australia, online and abroad. Maybe comparing Bitcoin against my credit card and cash is non-sensical. Maybe it’s really an investment, maybe it’s like shares. I think the best way to find out, is to buy some Bitcoin. A small amount to help me understand the technology….so where do I start? For me…the best place to start with any investment is to talk with my financial advisor….and this is where the problems started. Where can I buy Bitcoin, I asked and be confident that I’m receiving what I asked for…..ermmm…. nowhere. Why is that? Well…. if you go into the ANZ Bank and you want to buy currency…they have safeguards in the form of a specific financial legal acts that ensure you’ll get real currency and any charges are transparent. Currency is also easier to see, as it’s physical. When you go to a Bitcoin merchant, they’re not covered by any specific financial legal acts, so you can’t be 100% sure you are getting what you paid for. Also Bitcoins are virtual. It’s true you can see them in your virtual wallet, but there are no guarantees that you won’t be duped either in buying the Bitcoins or selling them. But if you assume that it’s more like shares, does that help. Well shares are listed on a stock exchange and are regulated by various acts in that country. The most well-known is the Sarbanes-Oxley ACT (SOX) which covers the listing of shares on the US stock exchange. Unfortunately for Bitcoin, it’s not covered by the same safeguards. So, what do I conclude…well I can buy Bitcoins from several merchants…but it’s difficult to assess what safeguards are in place, should I make a lot of money from the transaction. Anyhow…I’m happy with using my credit card and cash for purchases and I’m happy to continue investing in a balanced portfolio of shares, as well as using Netflix for kiddies’ films and Uber for rides into the city. Did I tell you about the time I discovered the Amazon Kindle and Agile Principles…….? This blog has been verified by Rise: Ra7540c712fcd526f20707909c6599ba8
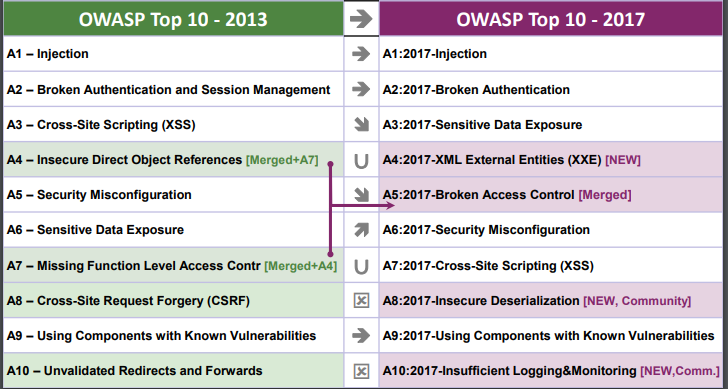
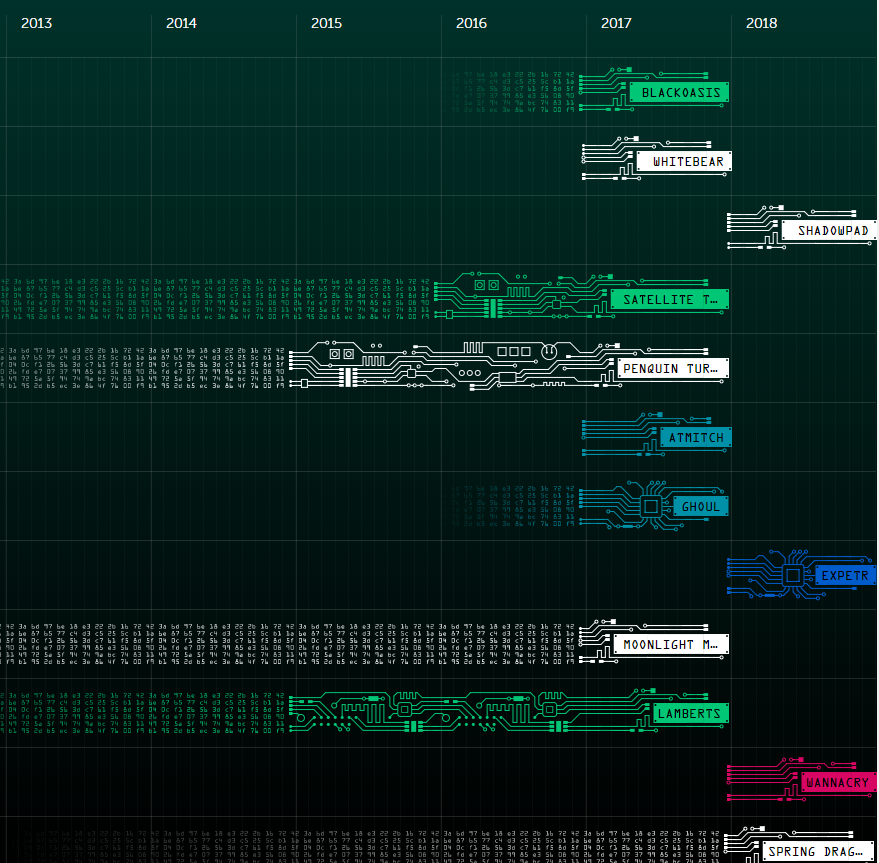
Today is my first day back as a cloud cyber coach in 2018. So I thought I'd start off the year with a quick revision of the Cloud Security Alliance Top #Cloud Threats, known as the Treacherous 12. This was updated to include specific real-life examples in November 2017: https://downloads.cloudsecurityalliance.org/assets/research/top-threats/Treacherous-12_Cloud-Computing_Top-Threats.pdf Followed by more revision of the OWASP Top 10 threats that are relevant when developing software, which was updated in 2017: https://www.owasp.org/images/7/72/OWASP_Top_10-2017_%28en%29.pdf.pdf This lead to me to refresh my memory on the most significant advanced persistent threat (APT) events of 2017, as well as the definition of an APT. So an Advanced Persistent Threat is a specialised and generally sophisticated attack that we often associate with CyberWarfare and Cyber espionage. It generally consists of installing malicious software onto a number of hosts into an organisation, orchestrated by a third party, and results in some form of damage to the infected organisation, i.e. credit card data being exposed (Sony) or data being destroyed via encryption (WannaCry). A found a great resource from Kaspersky Labs that provides a visual dashboard for all known APTs. https://apt.securelist.com/#!/threats/ Here are the Top 3 most dangerous threats found towards the end of 2017:
1 ShadowPad - A company called NetSarang produce server management tools for large corporate networks. Their products, available via download, had become infected with an encrypted payload from a malicious actor. Software should be removed and the latest 'clean' copies installed. https://securelist.com/shadowpad-in-corporate-networks/81432/ 2 NoPetya / ExPetr - This is ransonware which is spread via the use of custom tools, such as Mimikatz. It reboots the system after infection and starts to encrypt data onto NTFS partitions, which affects Windows PC's and servers. https://securelist.com/schroedingers-petya/78870/ 3 WannaCry - Well publicised in the media, this is also ransonware, and exploits a known vulnerability on Windows devices, called 'EternalBlue' . If your Windows devices are patched against EternalBlue exploit, then you're safe, however many organisation did not and were susceptible to WannaCry. https://securelist.com/wannacry-ransomware-used-in-widespread-attacks-all-over-the-world/78351/ |
CategoriesAll Active Directory AI Architecture Big Data Blockchain Cloud Comedy Cyber DevOps Driverless Cars MicroServices Office 365 Scaled Agile Social Media AuthorPaul Colmer is an AWS Senior Technical Trainer. Paul has an infectious passion for inspring others to learn and to applying disruptive thinking in an engaging and positive way. Archives
May 2023
|







 RSS Feed
RSS Feed