|
For the first time in 2018, it's become easier than ever to gauge the state of the cloud market. New data from the top cloud providers, mean we can really see who is dominating the landscape. In this blog, I've chosen to look at the total revenue as an indicator of success. Partly because it's easy to measure, but also because it given an indication of relative market opportunity and growth. This chart is taken from a great ZDNET article that was published earlier this year: www.zdnet.com/article/cloud-providers-ranking-2018-how-aws-microsoft-google-cloud-platform-ibm-cloud-oracle-alibaba-stack/ It clearly shows Microsoft as the dominant force, which I predicted would be the case back in 2016. My colleagues at DXC Technology will attest to that prediction. I think it's also a reflection on a number of compelling events that have materialised over the past few years:
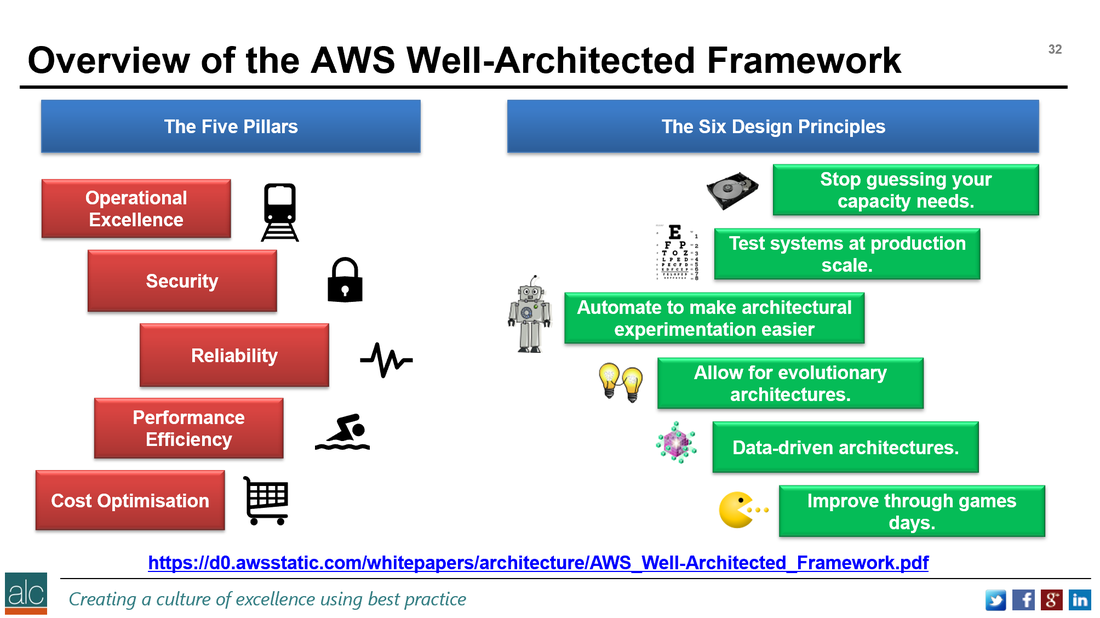
On the Amazon Web Services side, there is much progress and improvement especially in the area of new services. AWS are very good in the Serverless and PaaS spaces, adding a whole series of new innovations. These and exciting innovations were announced at the AWS ReInvent 2017 conference last year and include:
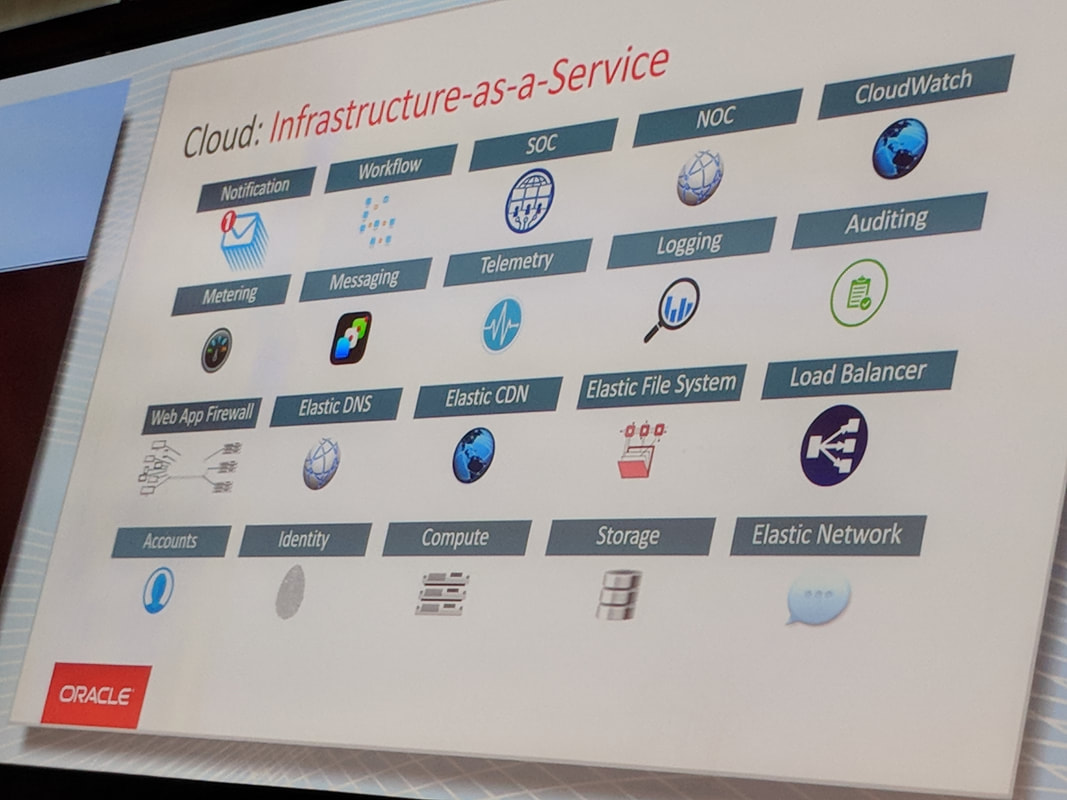
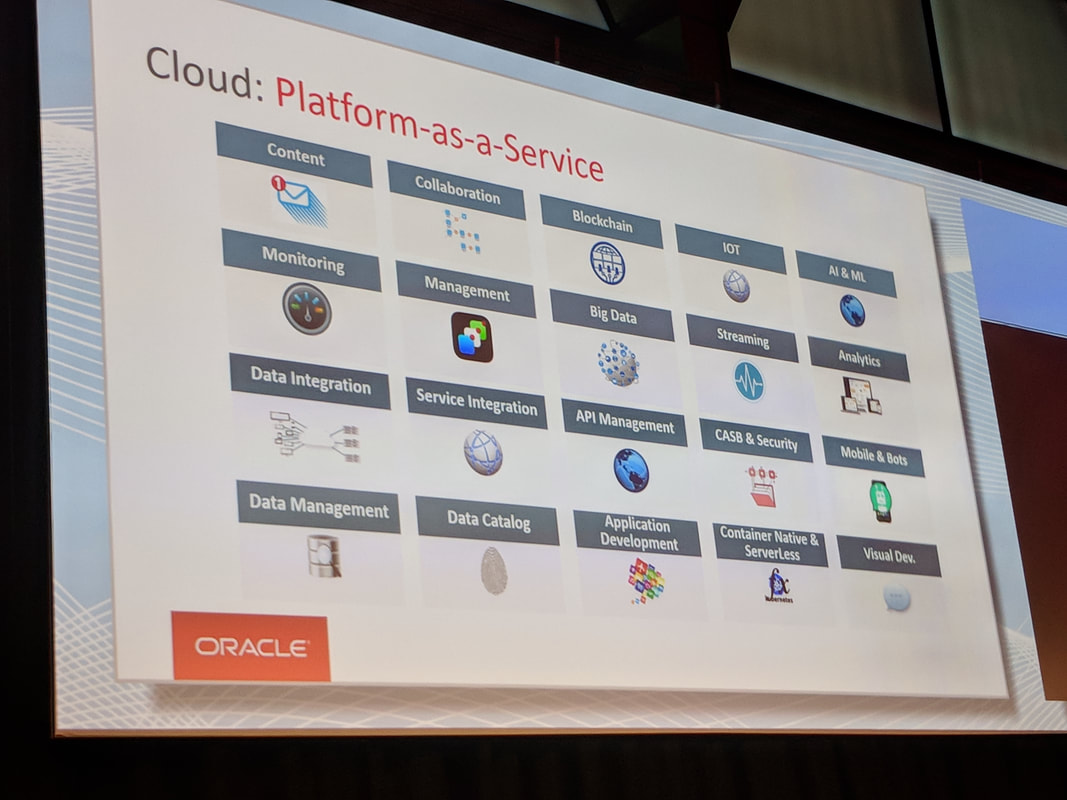
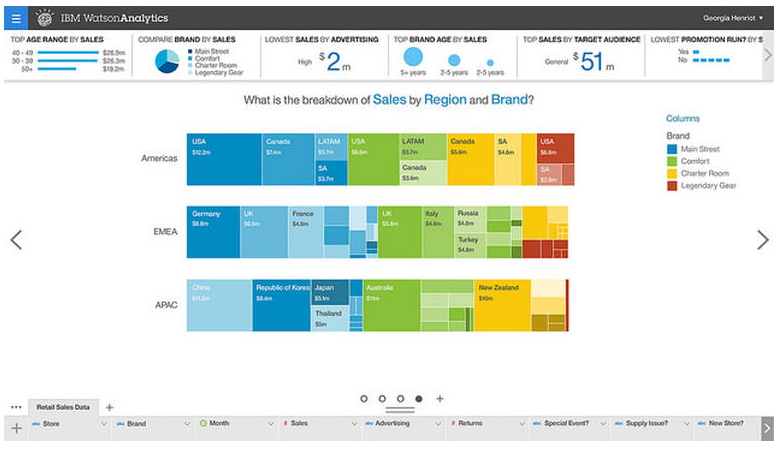
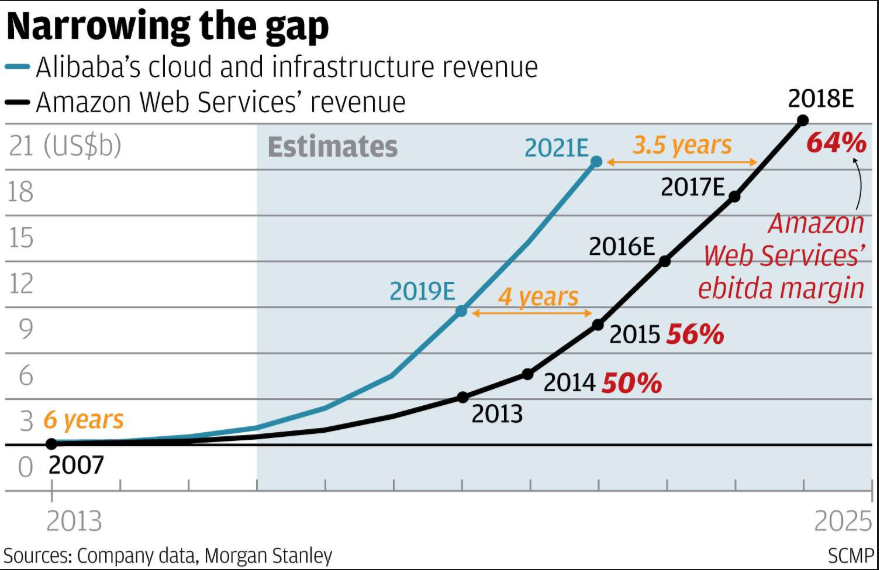
Oracle are coming up fast, probably as a result of their push in the past 12-18 months. A rep at Oracle invited me to attend Oracle Cloud World, which introduced me to the maturity and sleek look of their latest cloud offerings. The pics below gives a quick overview of the Oracle Cloud offerings: IBM is a little way behind the Top 2 leaders with their suite of cloud offerings. IBM Watson is probably the best known. I'm still waiting for IBM to approach me to, and invite me to their conference. Check out the screenshot below: More information on IBM cloud services can be found here: www.ibm.com/services/cloud?lnk=hpmse_ts&lnk2=learn Alibaba are a definitely one to watch. My prediction, is that by 2020 Alibaba will be No. 3 by revenue and may well be looking to eat up AWS with a takeover strategy, to compete with Microsoft. Here is a quick overview of the predicted growth of Alibaba revenue vs AWS: And here is a good article that articulates how large and dangerous Alibaba really is. I do apologise for all the popups, but the free content on the site IS worth the pain: www.cbinsights.com/research/amazon-alibaba-international-expansion/ The link below gives another perspective on the Microsoft / AWS revenue growth story, outlining some of the great customers stories to come out of the Azure platform. These include:
Finally if you feel you need some specialised training or business advice on AWS, Microsoft Azure, IBM, Oracle or Cloud CyberSecurity, feel free to reach out to me or to ALC Training: www.alctraining.com.au/courses/cloud-computing/ #CloudComputing #Cloud #AWS #Amazon #Microsoft #Azure #Office365 #CyberSecurity #CCSP #Training #Coaching #AI
0 Comments
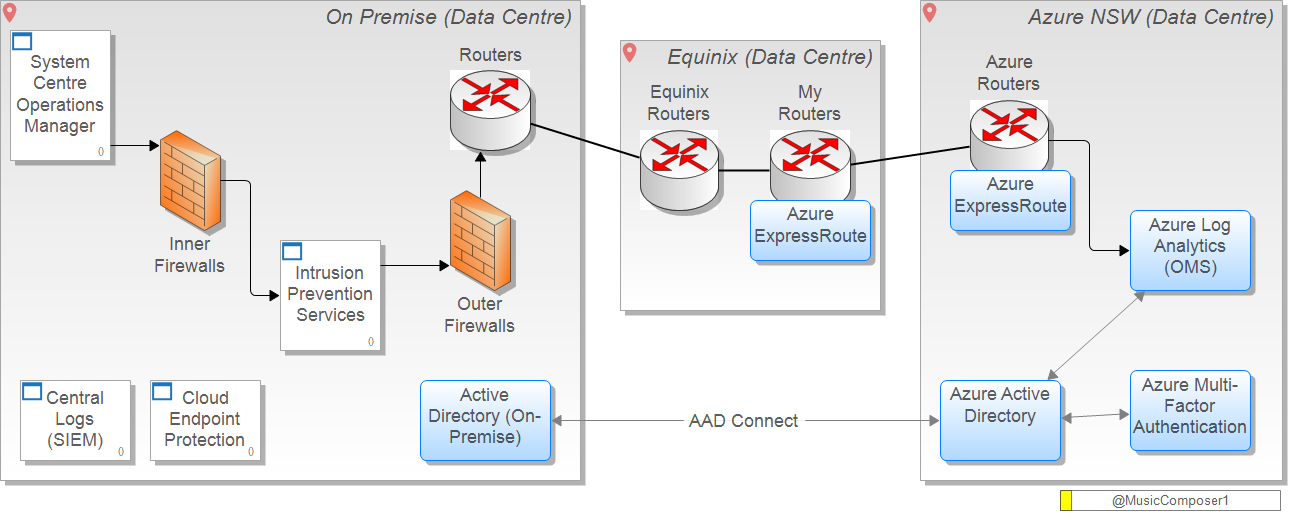
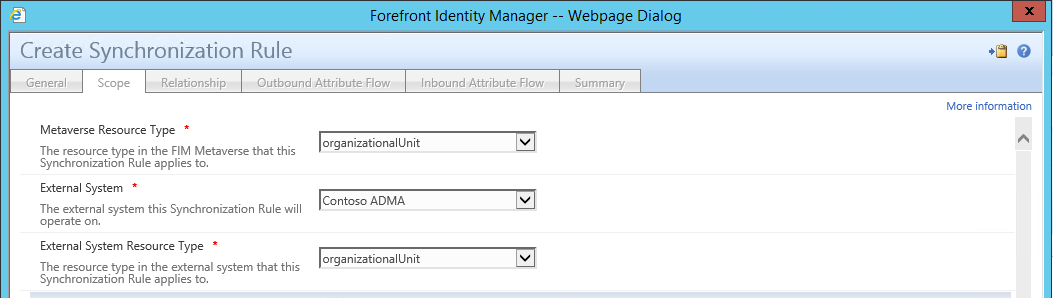
I had a fantastic question come through to me via twitter from a research student. He is doing a research thesis on access control mechanisms and wanted to know under what circumstances Microsoft Identity Manager (MIM) should be used over Azure Active Directory (AAD) connect. Firstly let's establish Azure Active Directory (AAD) is used for: https://docs.microsoft.com/en-us/azure/active-directory/connect/active-directory-aadconnectsync-whatis In a nutshell it allow you to create federated and synchronised contact information between one or many active directory domains with one or many Azure active directory domains. Here is an example of where you could use federation using AAD Connect. This is part of a wider architecture that allows you to integrate your SCOM monitoring data with Azure Log Analytics in OMS, using multi-factor authentication: The predecessor to Microsoft Identity Manager is Forefront Identity Manager, known as FIM, and with mainstream support ending in October this year and end of life expected in 2022: https://blogs.technet.microsoft.com/iamsupport/2017/02/22/warning-forefront-identity-manager-fim-mainstream-support-is-ending-10102017/ MIM has all the features of FIM plus a few more. Here is a great overview of MIM, which builds on the existing FIM features: https://docs.microsoft.com/en-us/microsoft-identity-manager/microsoft-identity-manager-2016 From my own experiences with FIM, MIM and AAD Connect, my thoughts are that it depends on the specific level of control you need. For example, if you have customised your Active Directory schema heavily and you have apps in your forest that use these customised data items, then you'll likely need more control and flexibility with your on-premise AD to Azure AD data synchronisation settings. Especially if you decide to move or migrate the apps that are utilising the custom meta-data, to the cloud. Another use-case is if you wish to use one of the inbuilt connectors to help federate between internal systems and AD on-premise. FIM comes with 3 connectors for example:
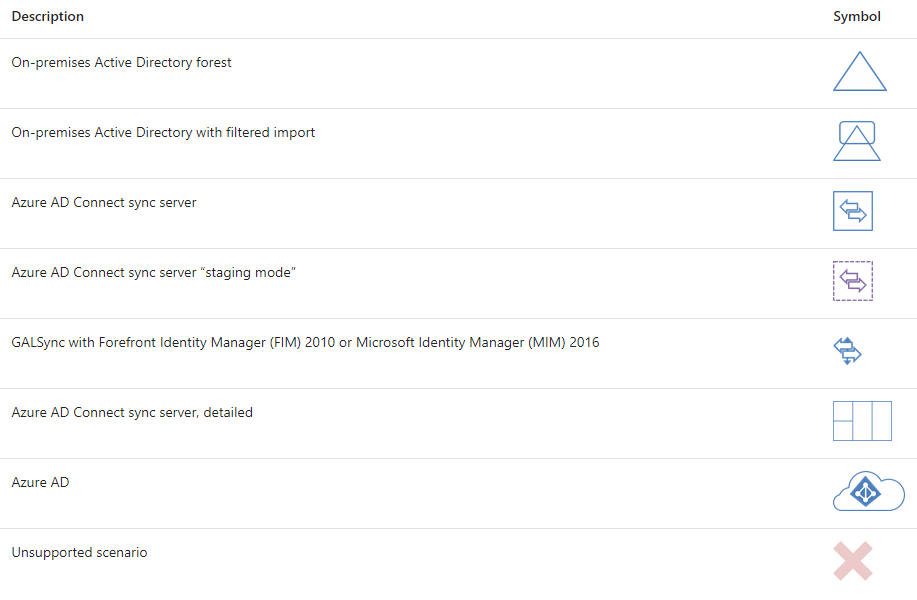
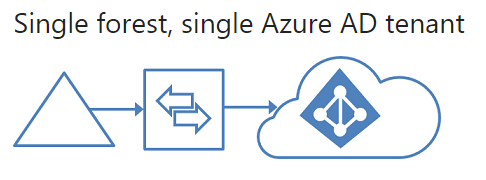
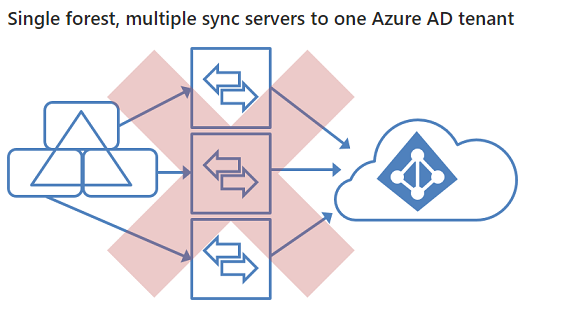
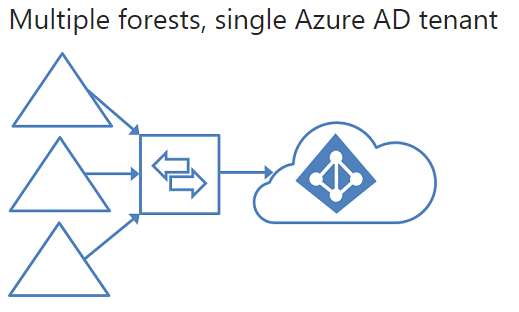
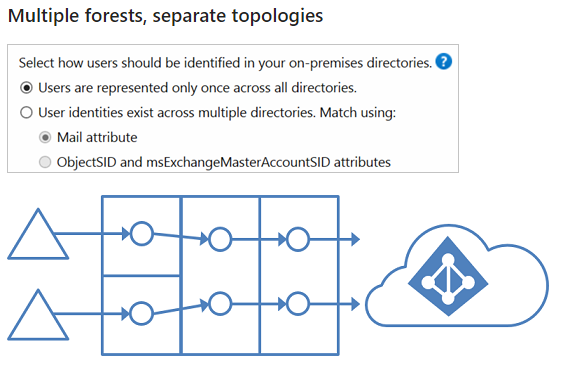
Microsoft Identity Manager does a great job of allowing you set custom synchronisation rules to provide that level of granularity. This article is based on the FIM sync rules, but still applies to MIM: https://blogs.msdn.microsoft.com/connector_space/2014/12/24/introducing-synchronization-rules-part-1/ Unfortunately, AAD Connect is also a moving target with features being constantly released that make it less feasible to use MIM. After a bit of digging around to find out the specific use cases, I found this great article on TechNet: https://docs.microsoft.com/en-us/azure/active-directory/active-directory-hybrid-identity-design-considerations-tools-comparison It clearly outlines all the key features that AAD currently support and that FIM supports. As you can see there are many features that are marked in AAD as 'future release'. But at the time of writing the following features were only supported with MIM: I also found this incredible resource, with outlines very clearly all the architectural patterns that are supported with AAD Connect: https://docs.microsoft.com/en-us/azure/active-directory/connect/active-directory-aadconnect-topologies#staging-server And here are some of the diagrams from the link showing the various patterns. If there is a red X shown it's an unsupported pattern: And there you have it. A very quick summary of resources that will help you decide whether to go AAD Connect or MIM for your organisation.
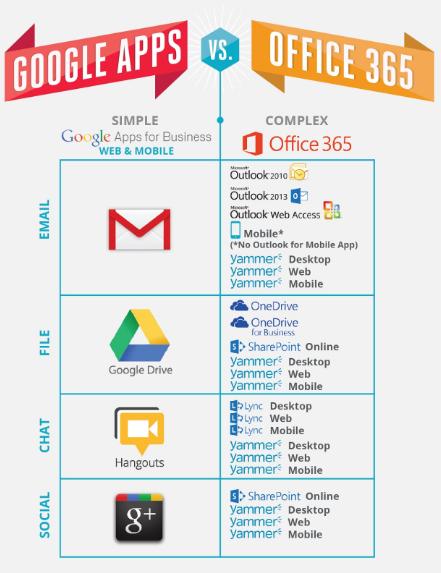
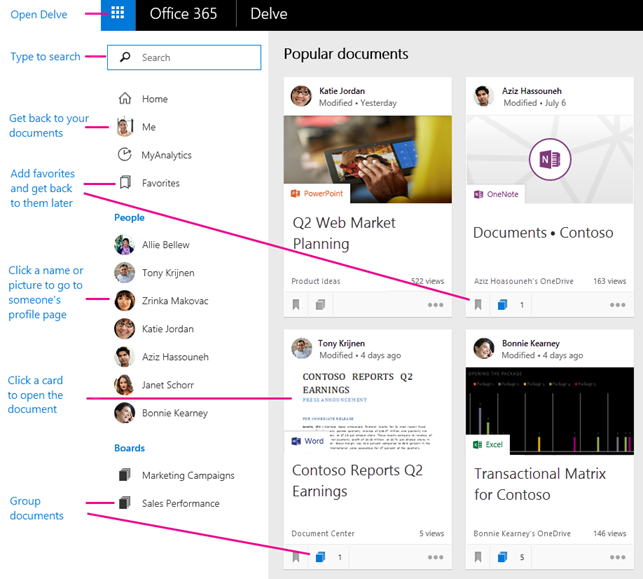
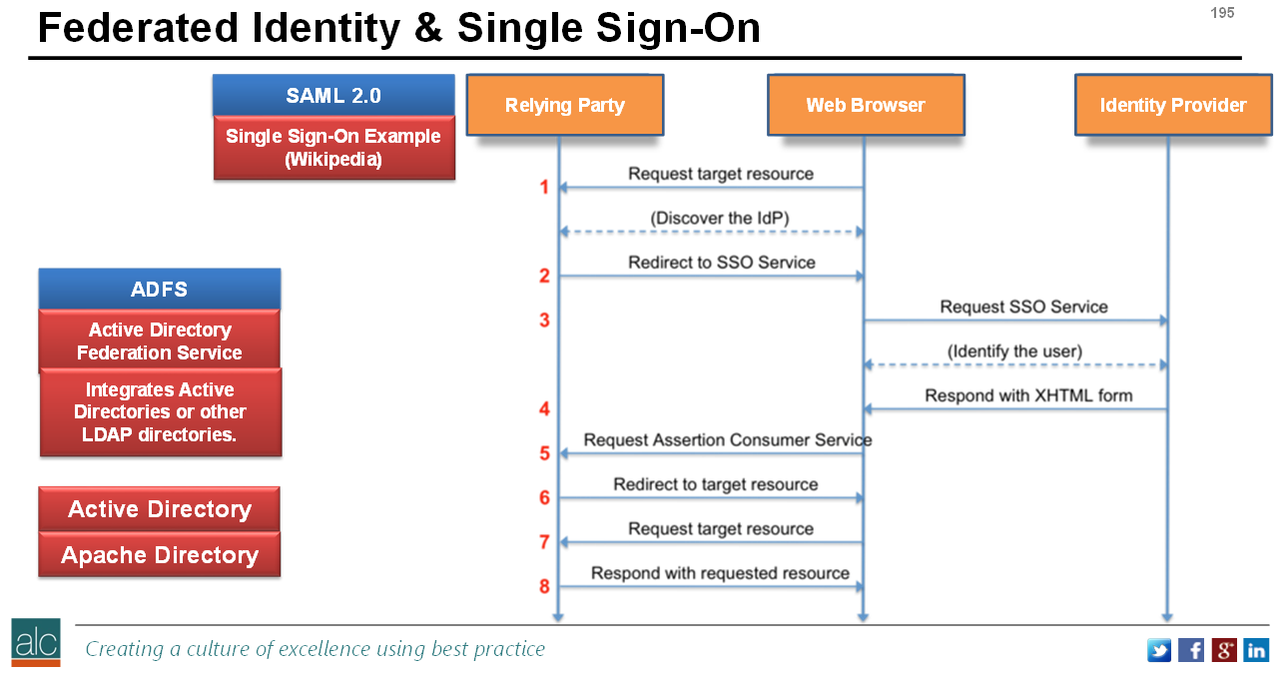
I always recommend the to start with a test setup of AAD Connect and a copy of your on-premise AD and simply identify several different use-case scenarios that you currently encounter. I think it's most likely that 90% of the time AAD Connect will be enough. The 10% being service providers hosting multiple clients with complex active directory requirements, or companies that have 100's of domains spread across several countries, with connections to internal systems for advanced identity federation. And yes, some clients really do have 100's of domains….. Paul Colmer is the lead digital architect ALC Training and Consulting. He is responsible for creating and running all the cloud security courses, which include CCSP, AWS, Azure, Office 365 and cloud foundation certifications. For more information visit: ttps://www.alctraining.com.au/courses/cloud-computing/ Or engage with Paul on his crazy adventures on twitter: @musiccomposer1 using the hashtag #CCSP As a Certified Cloud Security Professional (CCSP), one of the most common cloud services that I encounter across both the consumer and business worlds is the Microsoft Office 365 suite of services. It is classed as a Software-as-a-Service and it provides a graphically driven user-interface that enables businesses to send emails, collaborate, create and share intellectual property both within their organisation and with their key external partners. Here is a quick overview of the services. Now, if you've happily signed up to a simple home plan, you'll likely only have access to the Office Pro Plus Apps, which we have all known and loved for years. Apps such as Excel, PowerPoint, Word etc… But if you're running a business with say 100+ users, you'll probably already using the Office 365 Enterprise E1 subscription, which includes the Pro Plus Apps, plus the suite of cloud services. These cloud services will likely include Email, Contacts, SharePoint and many others, including Azure Active Directory. The diagram below shows a screenshot of a lesser known service called Delve: This is a great illustration of how Microsoft is innovating by allowing users to intuitively view and find data that they have access to, that may have been shared by colleagues. The Active Directory federation keeps all the data in a single synchronised entity , which allows services such as Delve to work efficiently and present a single source of truth to the end-user. This means if you're using an existing on-premise Active Directory service, with your servers housed in a data centre, or possibly in your small office, and are now using Office 365 services, you now have two Active Directories to worry about. This means your users are already logging into your company Active Directory to gain access to their files in your office, and then having to login again to gain access to the Office 365 resources. This is where directory federation, in this case Active Directory federation, adds huge value to end-users. By federating the two Active Directories together, you create a single logical security entity that provides huge user-experience benefits:
For example if you now wish to add Multi-Factor authentication (MFA) as a second security step when users are logging in, it is straight forward to integrate the Azure MFA with your Azure Active Directory, resulting in a 2nd step in the process that requires users to click accept on the Azure MFA app on their phones. The Azure MFA is easy to download and install and simply requires the user to establish their identity, the first time they use it.
Paul Colmer is a lead digital architect and cloud instructor for ALC training and consulting: www.alctraining.com.au/courses/cloud-computing/ |
CategoriesAll Active Directory AI Architecture Big Data Blockchain Cloud Comedy Cyber DevOps Driverless Cars MicroServices Office 365 Scaled Agile Social Media AuthorPaul Colmer is an AWS Senior Technical Trainer. Paul has an infectious passion for inspring others to learn and to applying disruptive thinking in an engaging and positive way. Archives
May 2023
|





 RSS Feed
RSS Feed